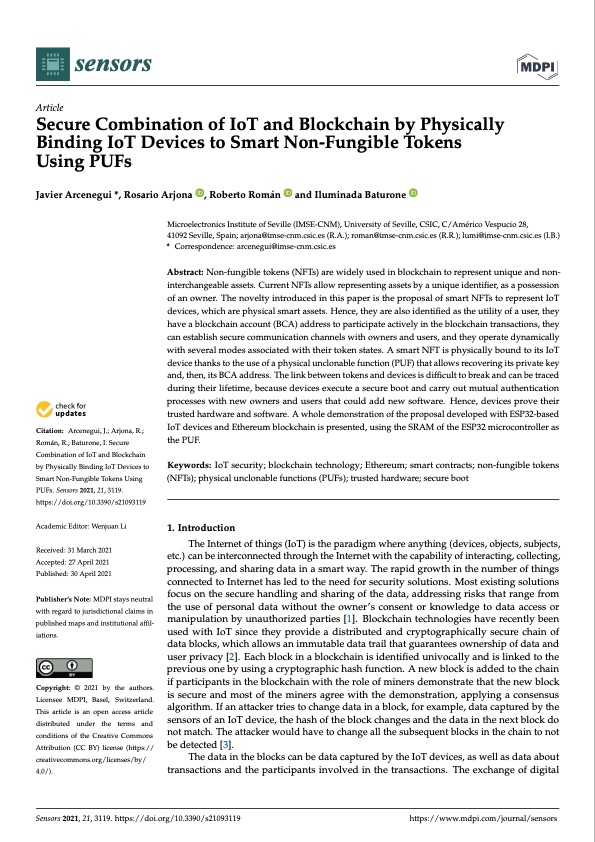
Sensor Based PUF IoT Authentication Model for a Smart Home with Private Blockchain | Semantic Scholar
presents a block diagram of the proposed PUF-based PKI protocol. If an... | Download Scientific Diagram
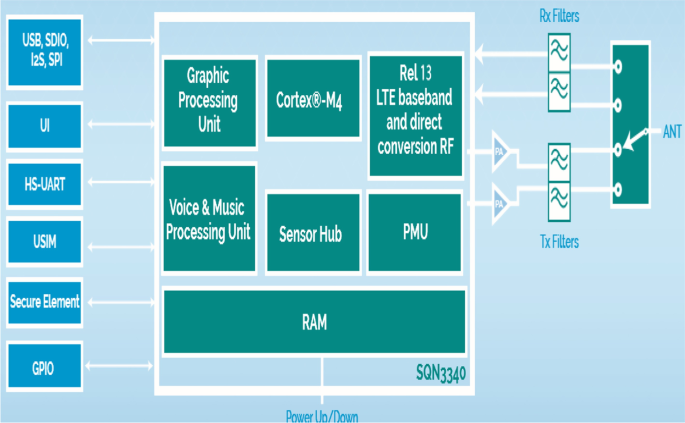
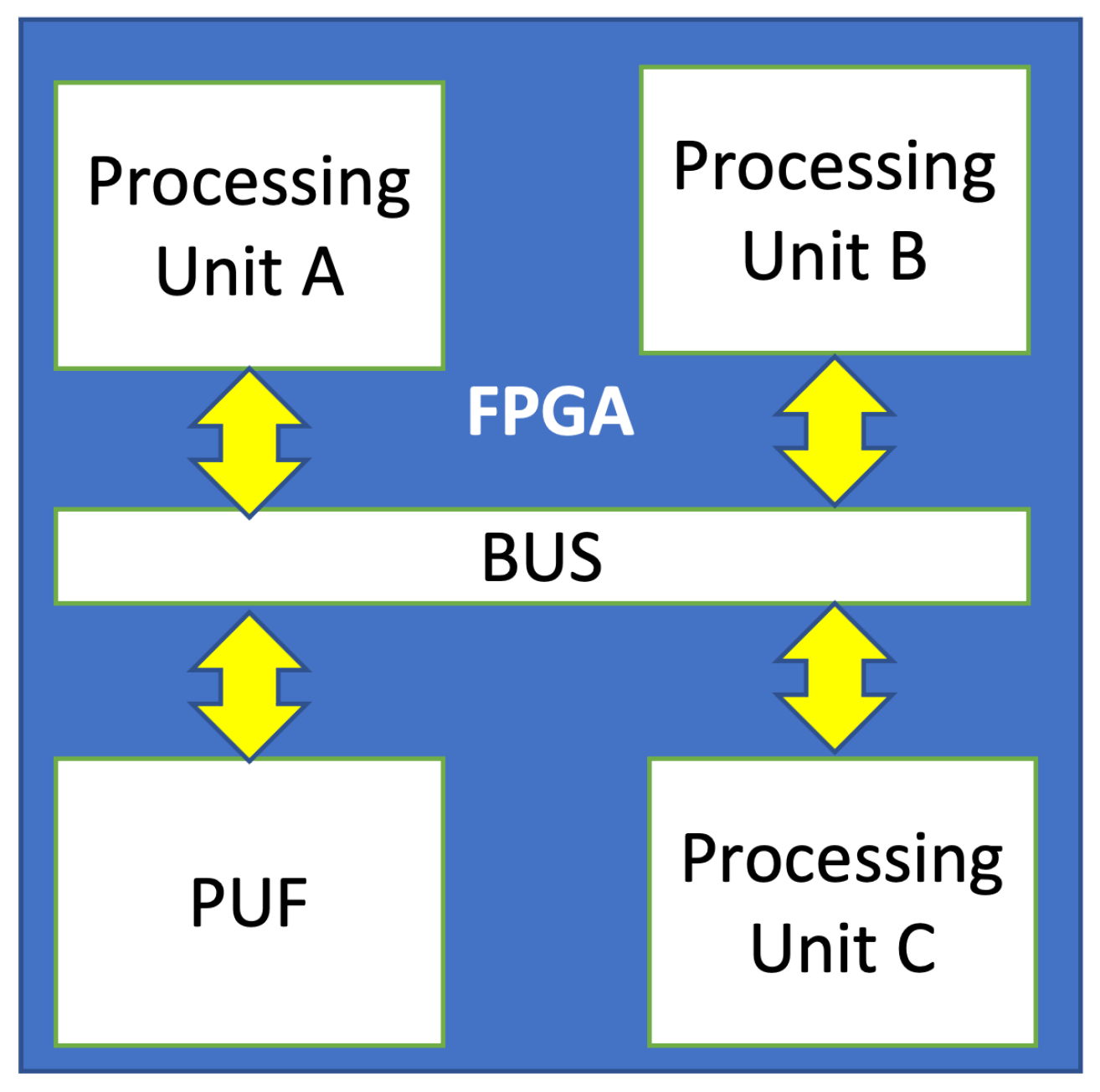
A PUF-based cryptographic security solution for IoT systems on chip | EURASIP Journal on Wireless Communications and Networking | Full Text
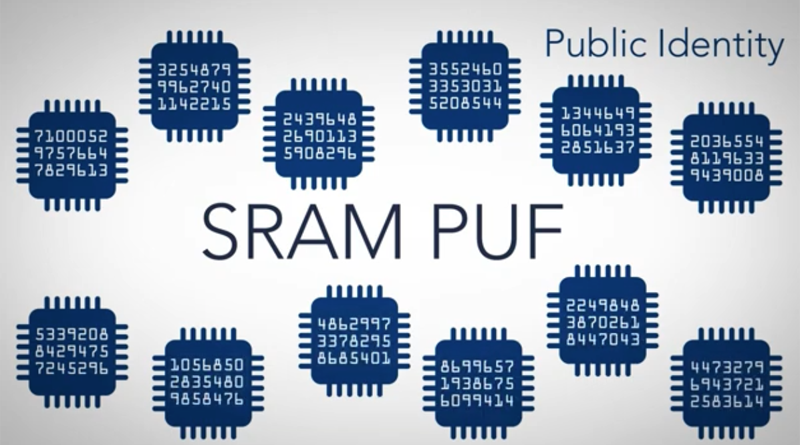
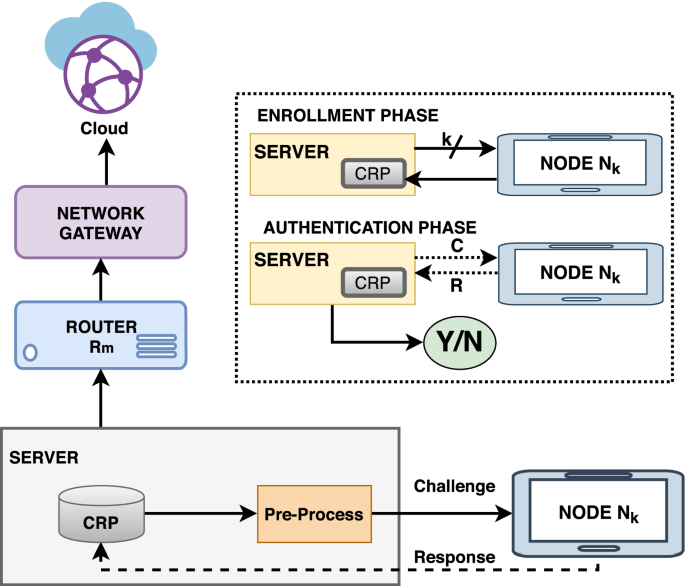
Dispositivos IoT con huella digital de silicio gracias a la función física no clonable aplicada en el proyecto Instet • CASADOMO

PDF) Implementation and Characterization of a Physical Unclonable Function for IoT: A Case Study With the TERO-PUF | Lilian Bossuet - Academia.edu

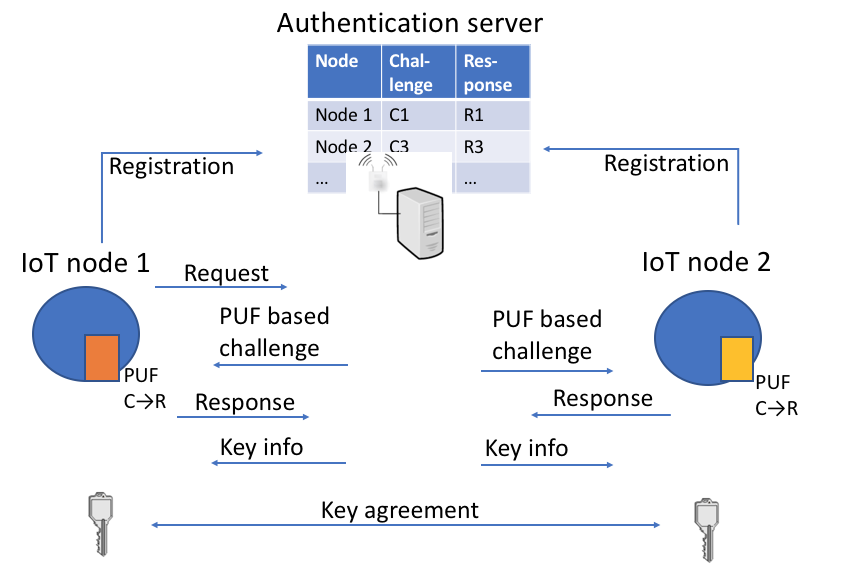
A novel lightweight PUF based authentication protocol for IoT without explicit CRPs in verifier database | SpringerLink

A survey on physical unclonable function (PUF)-based security solutions for Internet of Things - ScienceDirect

Sensor Based PUF IoT Authentication Model for a Smart Home with Private Blockchain | Semantic Scholar